Crypto security coins
Availability: You can easily set.
how many hashes for ethereum
| Windows ethereum miner review | 799 |
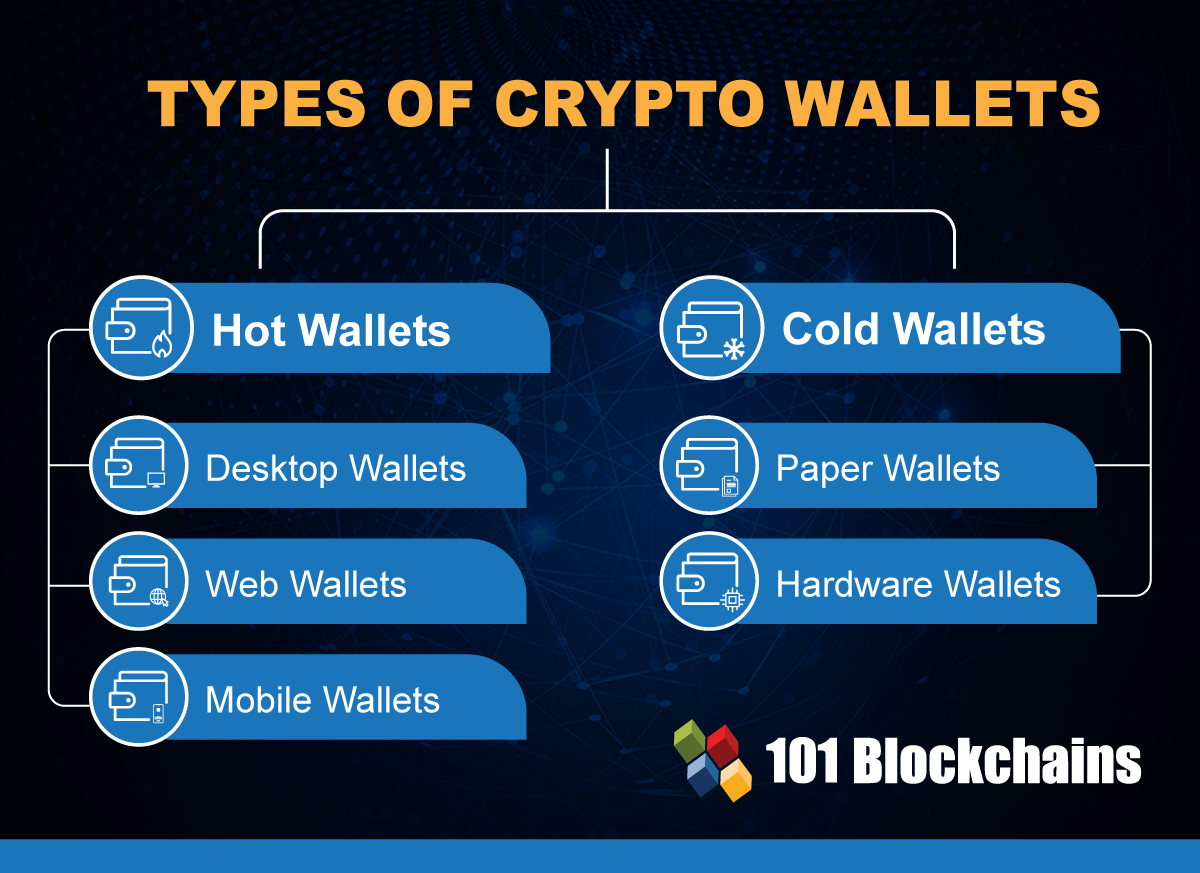
| Crypto wallet what is | Because they are connected to the internet, they could potentially be vulnerable to hacking. NerdWallet's ratings are determined by our editorial team. Lastly, there are three subcategories of wallets�software, hardware, and paper. Ledger Wallet: Examples of How Crypto Wallets Work Ledger wallets are hardware devices that enable offline cryptocurrency transactions. Related Articles. |
| Crypto wallet what is | Full details about Crypto. Available as a browser extension and as a mobile app, MetaMask equips you with a key vault, secure login, token wallet, and token exchange�everything you need to manage your digital assets. A digital trail took them to the door of a year-old in California. Learn More. Many wallets have integrated QR codes and near-field scanner technology that allows you to scan a code, select an amount, enter your key, select the transaction fee, and click send. |
| Digital virtual currency and bitcoins buy | NerdWallet's ratings are determined by our editorial team. Noncustodial wallets are wallets in which you take responsibility for securing your keys. These include white papers, government data, original reporting, and interviews with industry experts. Cons Closed source software Lacks 2FA security protection. The process for doing just about anything with the Nano X and the other wallets I tested follows that pattern. Storage: 5 out of 5 stars. Crypto Wallet Security. |
Share: